What is Firewall ?
A network firewall is a security system that protects private networks from unauthorized access. It monitors and controls incoming and outgoing traffic based on predefined security rules. It acts like a security guard, filtering data packets to either:
- Drop: Block silently without response.
- Accept: Allow the traffic.
- Reject: Block with an error response.
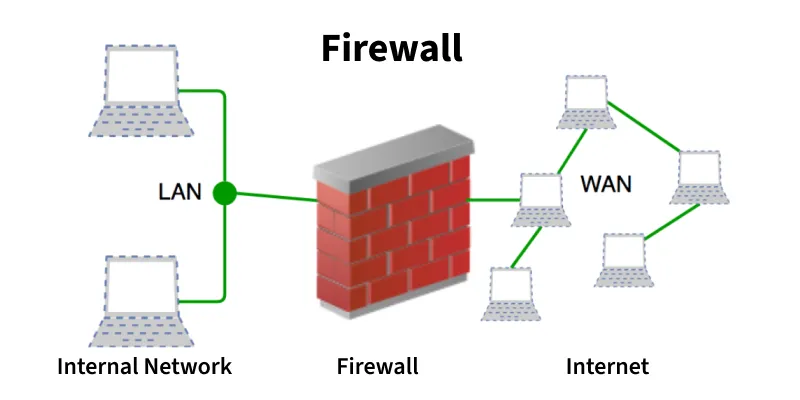
- Acts as a barrier between internal (trusted) and external (untrusted) networks
- Can be hardware-based, software-based, or both
- Filters traffic using rules, policies, and inspection methods
- Main goal: prevent attacks, malware, and unauthorized access
Types of Network Firewalls
Based on Functionality (How they filter traffic)
- Packet Filtering Firewalls: The most basic and oldest type. They inspect individual packets of data against a set of predefined rules (like IP addresses, ports, and protocols) and block or allow them. They do not consider the context of the traffic, making them fast but vulnerable to sophisticated attacks.
- Stateful Inspection Firewalls: Also known as dynamic packet filtering. These go a step further by monitoring the state of active connections. They remember the context of the traffic (e.g., if an incoming packet is a response to an outgoing request) and use this state table to make more intelligent filtering decisions.
- Proxy Firewalls (Application-Level Gateways): These operate at the application layer of the OSI model. Instead of letting traffic flow directly through, the proxy acts as an intermediary. It intercepts the connection, inspects the payload (the actual content of the data, not just the headers), and then establishes a new connection to the destination if the traffic is deemed safe.
- Next-Generation Firewalls (NGFW): These are the most advanced and widely used in modern enterprise environments. They combine traditional firewall capabilities (like stateful inspection) with advanced features such as deep packet inspection (DPI), intrusion prevention systems (IPS), encrypted traffic inspection, and application awareness/control.
- Circuit-Level Gateways: These work at the session layer. They quickly verify the Transmission Control Protocol (TCP) handshake to ensure the session is legitimate. While highly efficient and fast, they do not inspect the actual data packets themselves.
Based on Placement and Implementation (Where they live)
- Hardware Firewalls (Network-Based): These are physical, standalone appliances placed between the external network (internet) and the internal network. They protect the entire network boundary and have their own dedicated computing resources, so they don’t slow down individual computers.
- Software Firewalls (Host-Based): These are applications installed directly on individual computers or servers (the “host”). They protect that specific device by monitoring its specific incoming and outgoing traffic. Examples include Windows Defender Firewall or macOS Application Firewall. They are crucial for protecting devices when connected to untrusted networks (like public Wi-Fi).
- Cloud Firewalls (Firewall-as-a-Service / FWaaS): These are hosted entirely in the cloud and maintained by a third-party vendor. They provide scalable security for cloud-based infrastructure and remote workforces, eliminating the need for physical hardware on-site.